This is the thirteenth security tip from Laravel Security in Depth.Subscribe to receive weekly security tips and monthly In Depth emails covering Laravel Security topics. Passwords are the digital keys that keep user accounts safe, but passwords only work when they are secret and unguessable. The classic “fix” is to impose password complexity rules, but […]
Category: Security
This is the tenth security tip from Laravel Security in Depth.Subscribe to receive weekly security tips and monthly In Depth emails covering Laravel Security topics. When committing changes into version control, you should always selectively stage your changes first before committing. This allows you to manually review every line of code you commit, to ensure […]
This is the seventh security tip from Laravel Security in Depth, which was sent out on November 9th. You can subscribe to receive more tips and monthly In Depth emails covering of Laravel Security. Don’t trust user input. Don’t trust user input. And one more for good measure… Don’t trust user input. You should always […]
This is the fourth security tip from my Laravel Security in Depth newsletter, sent out to all subscribers on October 8th. Please subscribe if you’d like these tips delivered weekly. Laravel provides an expressive fluent interface for building database queries, either as raw queries through the query builder or as part of Eloquent (Laravel’s Object-Relational Mapper, ORM). The query builder allows […]
This is the first security tip from my Laravel Security in Depth newsletter, sent out on Monday to all subscribers. Please sign up if you’d like these tips delivered weekly. Laravel allows you to cast model attributes as encrypted strings, when stored in the database. This gives you added security for any values that are […]
Introducing Laravel Security in Depth

I started Laravel Security in Depth as a way to share my security knowledge with the Laravel community, and have a lot of fun doing so. My goal is to provide a community for everyone, regardless of their skill level and prior experience in security, where you can learn new things and ask questions, and learn to […]
The often talked about security risk of using SMS-based Two Factor Authentication (2FA) isn’t actually as big of a security risk that everyones makes it out to be. It’s much more of a security risk in SMS-based Account Recovery. It’s a subtle but incredibly important difference that I keep seeing news sites and security blogs completely overlook. […]
My wife and I¹ were filling out a rental house application the other night, and we noted the incredibly invasive nature of the personal information the form was asking for. For example, it wanted to know our car registration number and pet microchip details – both of which have absolutely nothing to do with us […]
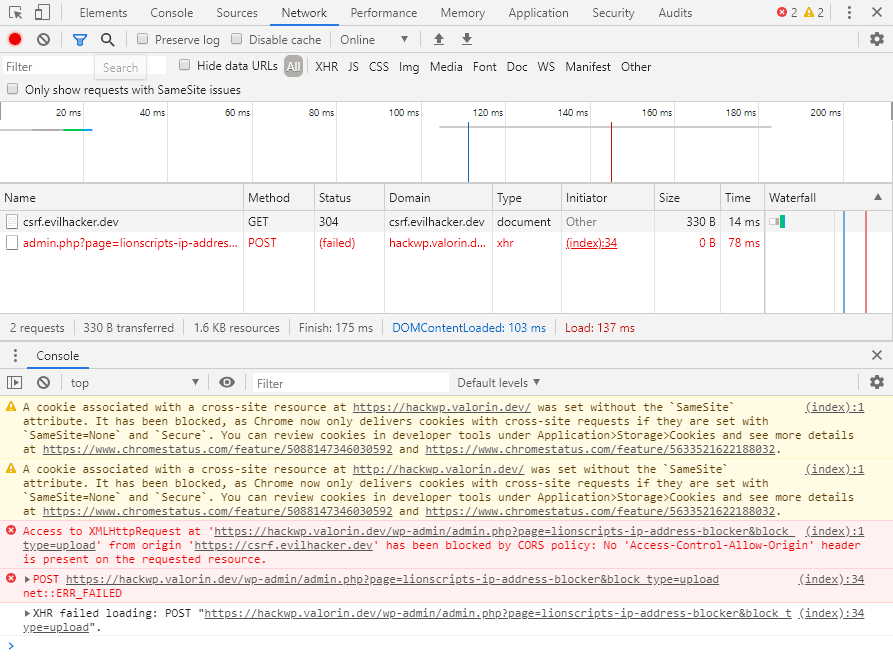
In the original version my talk “Think Like a Hacker and Secure WordPress, live on stage“, I demonstrated a Cross-Site Request Forgery (CSRF) attack. While this attack worked perfectly during WordCamp Brisbane 2019, in-progress changes to Google Chrome (version 80) are bringing about the end of CSRF. (Well, sort of…) In light of this change, […]
Usernames Are Not Secrets

A common misconception that I have observed a lot online is the belief that usernames should be secret, unique and hard to guess. While there are some limited cases where having a secret username is a good idea, most of the time it has no real benefit. Usernames are not secrets and should not be […]